
N3/HSCN *.nhs.uk email domains can use the Email Gateway by configuring their Message Transfer Agents (MTAs) to route traffic to/from the Email Gateway.
The Email Gateway should always be used for nhs.uk to nhs.uk message transfer to provide additional anti-virus and anti-spam protection to your email traffic over and above your own local protection.
The Email Gateway checks all outbound messages for SPAM and attempts to prevent both SPAM and malicious files/attachments from being sent. SPAM and malicious email are not the only cause of deny-listing. Deny-listingcan happen due to the following:
Automated Email Bounce Backs – N3/HSCN based *.nhs.uk organisations sending automated emails to external recipients must monitor bounce backs. The higher the number of undelivered (bounced back) email from the Email Gateway, the higher the potential the Email Gateway would be categorised as a spamming source. It is vital that any automated mailing facility has a process in place to check and remove bounced email from mailing lists.
Compromised Accounts – A compromised account has the ability to send SPAM or malicious email. These emails (due to coming from a semi-trusted source on the N3/HSCN), may have been able to send several emails through the Email Gateway before being classified as SPAM (or malicious). It is important that local organisations monitor email locally for suspicious activity and ensure only warranted communications are sent to the Email Gateway.
Compromised Systems – Locally compromised systems can themselves be sources of spam or malicious email, or can lead to compromised accounts. All N3/HSCN based organisations should have security policies, antivirus, and system monitoring in place to minimise the likelihood of compromised systems.
For the domain nhs.uk, the Email Gateway support up to 3 levels of sub-domains for email transfer. No subdomains should be used to send or receive emails greater than 3 subdomains deep. The below example will illustrate the sub-level support of the email gateway for the domain *.nhs.uk:
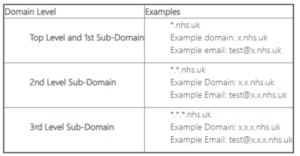
Any sub-levels greater that 3 (as illustrated above), are not supported and may be rejected by the Email Gateway service.
The Email Gateway tracks SPAM and malicious files from N3/HSCN based organisations. If these organisations send large volumes of SPAM or malicious files to the Email Gateway, the Email Gateway will block the offending organisation at the internet protocol (IP) level from sending any mail for up to four hours. This block is done to protect the greater base of N3/HSCN *.nhs.uk organisations who rely on the Email Gateway.
The Email Gateway monitors the volume of email sent from all accounts. This monitoring is in place to protect against the potential of compromised accounts, compromised systems and ultimately the deny-listing of the Email Gateway. If there is an account designated to send high volumes of email, please contact the Email Gateway helpdesk@nhs.net for the account to be added to a high-sender allow-list.
Data transmitted across the Relay Service is not guaranteed to be encrypted end to end or meet the national encryption cipher requirements. Thus the Relay Service is not considered secure enough to transmit patient identifiable or similarly sensitive data across. It does not meet the Caldicott Guidelines requirements alone. It is the joint responsibility of the sender(s) and receiver(s) of such data to implement a solution that conforms such as suitably encrypted messages that provide end to end integrity.
Email service mailbox to external gateway is 95% delivered within 3 minutes or less. External gateway to email service mailbox is 95% delivered within 3 minutes or less.
As a Local Email Administrator, you should set a transport rule so that any junk / spam emails received are delivered to the end user’s junk email folder by default. Any junk / spam emails that pass through the NHSmail or the Relay service always have the following header information – “X-SPAM-JUNK-FOLDER: TRUE”.
Why do I receive the following response from Email2SMS “1 033 ERROR – the request is not authenticated” while sending SMSs from my NHS.NET account? This error message indicates that the NHS.NET user is not allow-listed on Soprano. User needs to contact their local administrator who in turn would need to contact Soprano (support@tailored.bt.com) and request them for the NHS.NET address to be allow-listed.
| Last Reviewed Date | 23/07/2024 |
